On Thursday, March 20, an attacker known as rose87168 published several text files containing a sample database, LDAP information, and a list of companies that, according to the attacker, were victims of a massive data theft from the SSO (Single Sign-On) platform of Oracle Cloud.
Despite the attacker’s claims, Oracle has denied suffering a data breach, asserting that the published credentials do not belong to Oracle Cloud’s infrastructure and that no clients of the platform suffered data loss. However, controversy is rising after rose87168 shared additional evidence suggesting that the data may indeed originate from their servers.
Oracle’s Denial and the Attacker’s Evidence
According to Oracle, there has been no leak within their systems, countering the attacker’s claims, who was already offering the supposedly stolen data for sale, including 6 million records, among which are hundreds of domains from organizations in Latin America. To bolster their claim, the attacker shared a URL from Internet Archive that displayed having uploaded a .TXT file with their ProtonMail email address to Oracle’s login server: login.us2.oraclecloud.com.
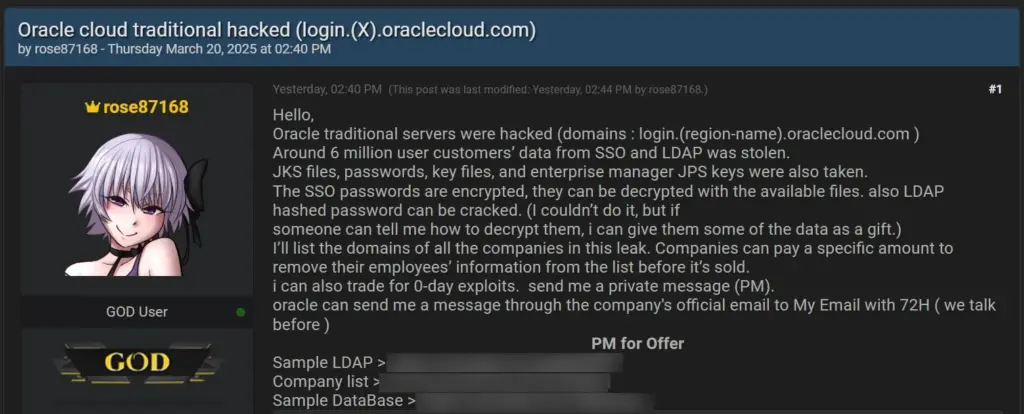
The attacker, rose87168, besides offering the data for sale, also stated that the SSO passwords were encrypted, but could be decrypted using the available files, as well as the LDAP hash passwords. rose87168 also promised to list all the domains of the involved companies and offered to remove specific information in exchange for payments or exchanges of Zero-Day exploits.
Examination of the Leak
On March 25, the attacker shared a sample of 10,000 lines to strengthen their claim, leading researchers to conduct a detailed analysis. The most relevant findings were as follows:
- Widespread Impact: The data sample contains records from over 1,500 organizations, suggesting a significant leak.
- Authenticity of the Data: The structure and volume of the leaked information make forgery difficult, reinforcing the validity of the leak.
- Possible Access to Production: Many of the records contain tenant IDs in formats like
{tenant}-dev,{tenant}-test, and{tenant}, suggesting that the attacker may have also had access to production environments. - Exposure of Personal Emails: The leak includes a significant amount of personal emails, likely due to organizations allowing SSO authentication for their employees and customers.
The cybersecurity company CloudSek has released a free tool that allows organizations to verify if they are on the list of victims shared by the attacker.
CVE-2021-35587 and the Exploited Vulnerability
The attacker also highlighted that Oracle Cloud is still using a vulnerable version with CVE-2021-35587, a critical vulnerability in Oracle Access Manager. This CVE (with a CVSS score of 9.8) allows an unauthenticated attacker to compromise Oracle Access Manager, which can lead to remote code execution (RCE) and total control over the system.
CVE-2021-35587 was published in January 2022 and affects versions of Oracle Fusion Middleware such as 11.1.2.3.0, 12.2.1.3.0, and 12.2.1.4.0, which are vulnerable to attacks due to this flaw. Since its discovery, public exploits have been developed for this vulnerability, and the attacker claimed to have used it to access Oracle’s servers.
Confirmation of the Leak
Oracle’s denial has been contradicted by researchers who received additional samples of the leaked data and confirmed the authenticity of the leak. Some representatives from the affected companies confirmed, on condition of anonymity, that the information included in the leak, such as names, email addresses, and LDAP data, was accurate and belonged to them.
Furthermore, it has been confirmed that the attacker maintained communication with Oracle, requesting payment in XMR (Monero) to provide details on how they exploited Oracle’s servers. An email exchanged with an Oracle employee, using a @proton.me address, shows an attempt to negotiate with the company following the leak.
Oracle’s Actions and Consequences
Oracle disconnected the compromised server after learning of the breach, and security experts have indicated that the Oracle Fusion Middleware 11g affected by CVE-2021-35587 allowed attackers to compromise Oracle Access Manager and access sensitive information. This incident highlights not only the severity of the vulnerability but also the urgent need to update and patch critical systems in cloud environments.
Final Reflection
The data leak affecting Oracle Cloud exposes the vulnerability of cloud platforms and underscores the importance of keeping systems updated and protected against cyber threats. This incident also highlights how security breaches can have far-reaching consequences, affecting thousands of organizations worldwide. Companies must take preventive measures to avoid becoming victims of such cyberattacks and mitigate the risks associated with known vulnerabilities like the mentioned CVE-2021-35587.
Sources: Segur Info, BC I, BC II, CloudSek I, and CloudSek II

