1. Introduction to End-to-End Encryption
End-to-end encryption (E2EE) is a security system that ensures that only the participants in a communication can read the messages, protecting them from interception by third parties, including service providers, hackers, and governments.
Unlike encryption in transit (such as TLS/SSL), where data can be decrypted by intermediate servers, E2EE ensures that the information is never accessible outside the devices of the sender and receiver.
1.1. Why is E2EE Important?
- Privacy: Prevents companies and governments from accessing your conversations.
- Security: Protects against Man-in-the-Middle (MITM) attacks and data leaks.
- Confidentiality: Ensures that only the legitimate recipient can read the message.
2. How Does E2EE Work?
2.1. Basic Mechanism
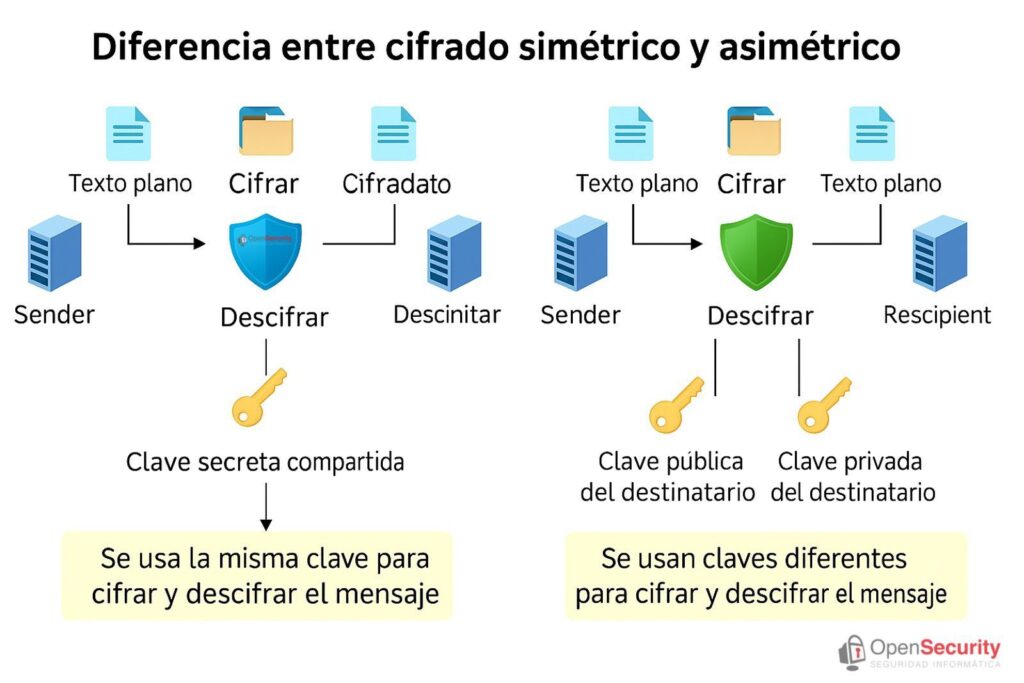
E2EE uses asymmetric cryptography (public/private key) and, in some cases, symmetric cryptography for greater efficiency.
- Key Generation:
- Each user has a key pair:
- Public key (shared with others to encrypt messages).
- Private key (secret, used to decrypt).
- Secure Exchange (e.g., Signal Protocol, Diffie-Hellman).
- Message Encryption:
- The sender uses the receiver’s public key to encrypt.
- The message travels encrypted through servers.
- Decryption:
- Only the receiver, with their private key, can read it.
2.2. Common E2EE Protocols
| Protocol | Used In | Advantages |
|---|---|---|
| Signal Protocol | WhatsApp, Signal | Considered the most secure |
| OMEMO (XMPP) | Jabber, Conversations | Encryption for federated messaging |
| PGP/GPG | Email (ProtonMail, Tutanota) | Old but robust standard |
| Matrix (Megolm) | Element, Matrix.org | Encryption for group chats |
3. Applications that Use E2EE
3.1. Instant Messaging
| Application | Type of E2EE | Enabled by Default? |
|---|---|---|
| Signal | Signal Protocol | ✅ Yes |
| Signal Protocol | ✅ Yes (except cloud backups) | |
| Telegram | MTProto (only in “Secret Chats”) | ❌ No (requires manual activation) |
| Threema | NaCL (libsodium) | ✅ Yes |
| Wire | Proteus (derived from Signal) | ✅ Yes |
3.2. Secure Email
| Service | Protocol | Features |
|---|---|---|
| ProtonMail | PGP + E2EE between users | Automatic encryption between Proton accounts |
| Tutanota | AES + RSA | Encryption even in subject and metadata |
| Mailfence | OpenPGP | Encrypted storage |
3.3. Voice and Video Calls
| Application | Encryption | Details |
|---|---|---|
| Signal | Signal Protocol | E2EE voice and video calls |
| Jitsi Meet | E2EE (with additional configuration) | Open-source, alternative to Zoom |
| Wire | Proteus | Encrypted group calls |
4. Comparison: E2EE vs. Other Types of Encryption
| Aspect | E2EE | Encryption in Transit (TLS/SSL) | Encryption at Rest |
|---|---|---|---|
| Who Can Access? | Only sender and receiver | Service provider can decrypt | Only with storage key |
| Use Case Example | WhatsApp, Signal | Gmail (not E2EE), HTTPS | iCloud, Google Drive |
| Protects Against Mass Surveillance | ✅ Yes | ❌ No (servers can read) | ❌ No (if provider cooperates) |
| Vulnerabilities | Loss of private key | MITM attacks, fake certificates | Theft of encryption keys |
5. Limitations and Risks of E2EE
5.1. Disadvantages
- No Data Recovery: If you lose your private key, you lose access.
- Exposed Metadata: Although the content is encrypted, it can be known who is talking to whom.
- Dependence on Implementation: If an app has bugs (e.g., Telegram with MTProto is not E2EE by default), security is reduced.
5.2. Can Governments Break E2EE?
- Theoretically no, but they can use:
- Backdoors (legally forced backdoors, such as in the case of the “Access to Data” law in Australia).
- Device Attacks (keyloggers, malware).
6. What Application to Choose? Recommendations
- Maximum Security: Signal (E2EE by default, open source).
- Email Privacy: ProtonMail or Tutanota.
- Group Chats: Element (Matrix) with E2EE enabled.
- Avoid if Possible: Telegram (no E2EE by default), Facebook Messenger (optional E2EE).
7. Conclusion
End-to-end encryption is the best way to protect digital communications, but it is not infallible. Its adoption in apps like Signal and WhatsApp has improved privacy, but there are still challenges in metadata and government coercion.
🔐 What E2EE app do you use? Share your experience!
Sources:

