The sovereign cloud has become one of the hottest buzzwords in the European tech market. Governments, regulated companies, and cloud providers use it to talk about data control, operational independence, and protection against foreign legislation. The problem is that it doesn’t always mean the same thing. CISPE, the association representing European cloud infrastructure providers, aims to bring clarity to this debate with the launch of its Sovereign and Resilient Cloud Services Framework.
The new framework, unveiled in Brussels during the EU Tech Sovereignty 2026 gathering by Francisco Mingorance, CISPE’s Secretary General, seeks to provide an auditable way to distinguish truly sovereign services, resilient services, and offerings that claim sovereignty without providing verifiable guarantees. The association summarizes this with a growing sector term: avoiding “sovereignty washing.”
A response to the confusing use of the word “sovereign”
The release comes at a particularly sensitive moment for Europe’s digital infrastructure. Dependence on large non-EU providers, regulatory pressures, advances in AI, and growing public cloud spending have made digital sovereignty a strategic issue. But at the same time, the market is flooded with offerings claiming to be sovereign because they operate in Europe, use European data centers, or meet cybersecurity standards—without those factors necessarily guaranteeing legal, operational, or technical independence.
CISPE argues that customers need to know whether a cloud service could be exposed to interference from foreign jurisdictions, risk interruptions, access blocks, or dependence on a provider. In its public communications, the association even uses the term “Trump Proof” services—an eye-catching way to refer to concerns about political or legal decisions by third countries that might impact digital services used by European organizations.
The framework doesn’t just ask where data is stored. Its goal is to assess effective control over data, infrastructure, workloads, and operations. This distinction is important because a cybersecurity certification can demonstrate that a service is well-protected against attacks or vulnerabilities, but not necessarily that it’s free from risks like legal dependence, commercial blocking, or irreversibility issues.
Sovereign and resilient services: two different paths
CISPE’s proposal introduces two complementary categories. On one hand, sovereign services, which seek to guarantee control by design. On the other, resilient services, which accept that some non-sovereign elements may exist but require technical and operational mechanisms to allow the customer to maintain control if a problem arises.
| Category | Meaning | Control Examples |
|---|---|---|
| Sovereign Service | Design control within a specific jurisdiction | Ownership, governance, and operation within the jurisdiction; protection against access, interference, or disruption by foreign powers |
| Resilient Service | Control based on capacity, even if non-sovereign dependencies exist | Client-managed encryption, portability, independent copies, reversibility, and the ability to switch providers or redeploy workloads |
| Optional Criteria | Additional indicators about the service | Use of open source software and environmental sustainability measures indicated through additional badges |
This distinction aims to address a common market tension. Not all organizations can currently access fully sovereign services for all their needs—especially when they require global scale, certain AI capabilities, specific software ecosystems, or integration with existing platforms. In those cases, CISPE suggests that resilience can be a valid alternative, provided the customer retains meaningful reaction capacity.
The association uses a simple analogy: sovereignty is like installing puncture-proof tires—preventing risk from the outset; resilience is more like run-flat tires, which allow continued driving even after an incident. This metaphor is for commercial purposes but helps clarify the approach: not all workloads require the same level of sovereignty, but all should be assessable with clear criteria.
Certification per service, not just per provider
One key aspect of the framework is that certification applies to specific cloud services, not to the company as a whole. This means a provider can’t broadly claim to be “sovereign” if only some of its services meet the criteria. Each service must go through its own process, with formal audit conducted by an accredited third party.
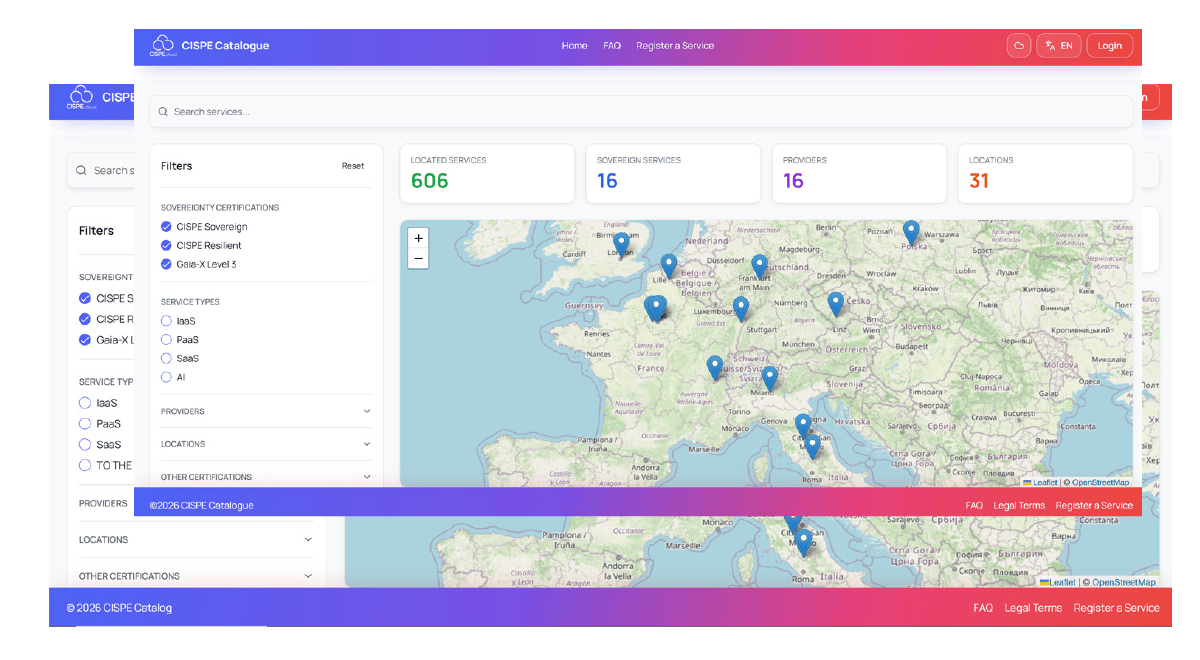
CISPE indicates that compliant services could receive specific badges and be listed in a public registry, making it easier for clients and governments to identify evaluated offerings. As of now, over 40 services have been declared under the new framework, including AI assistants, public cloud, Kubernetes, and storage solutions. The term “declared” is important: the real proof will lie in the depth of audits, transparency of the registry, and trust established with public and private buyers.
The framework also includes optional measures to reflect environmental sustainability and the use of open source software. These are not minor elements. In Europe, digital sovereignty often aligns with other political and industrial goals like reducing dependence on technology outside the EU, interoperability, transparency, energy efficiency, and strengthening the local ecosystem.
The sovereign cloud enters the European regulatory arena
The CISPE movement doesn’t act in a vacuum. The European Commission already developed its own Cloud Sovereignty Framework for procurement processes, aimed at strategic, legal, data, AI, operational, supply chain, technological, security, and environmental sustainability considerations. That approach uses levels of assurance and scoring to evaluate cloud offerings.
However, CISPE has been urging Europe for months to define sovereignty based on actual control rather than just presence on European soil or meeting security standards. As early as March 2026, the association called for the upcoming Cloud and AI Development Act to centralize the focus on sovereignty, resilience, and fair competition within European cloud policy. Their stance is clear: if the concept of a sovereign cloud is weakened too much, dominant non-European platforms could continue to control the market under new labels.
This position also has an industrial dimension. CISPE represents European cloud infrastructure providers and advocates for a framework likely to favor companies with ownership, operational control, and decision-making within Europe. This doesn’t invalidate their arguments but frames the initiative as part of a broader contest among European providers, U.S. hyperscalers, and governments balancing security, cost, innovation, and strategic autonomy.
The potential impact of the framework depends heavily on its adoption. If public administrations, regulated businesses, and major purchasers incorporate it into their procurement processes, it could become a key reference point for differentiating cloud offerings. Otherwise, if it remains a sector-specific initiative with little traction, its influence will be limited.
What seems clear is that the era of vague claims about “sovereign cloud” is coming to an end. In a market shaped by AI, provider consolidation, and geopolitical uncertainty, customers will demand more than promises—they’ll want details on who operates the service, under what jurisdiction, how dependent it is on external technology, what happens in case of outage, and how they can recover or move workloads.
CISPE’s innovation aims precisely at that: turning digital sovereignty into something measurable, auditable, and comparable. The challenge will be proving that the framework doesn’t add another layer of complexity but instead provides a practical tool for making better-informed decisions.
Frequently Asked Questions
What is the CISPE Sovereign and Resilient Cloud Services Framework?
It’s a framework developed by CISPE to evaluate, audit, and distinguish sovereign and resilient cloud services. Its goal is to help companies and governments verify whether a service provides real control over data, infrastructure, workloads, and operations.
What’s the difference between a sovereign and a resilient cloud?
A sovereign service aims to prevent risks from the outset through design, with ownership, governance, and operation within the relevant jurisdiction. A resilient service accepts external dependencies but requires controls such as client-managed encryption, portability, independent backups, and the ability to switch providers or redeploy workloads.
Does a cybersecurity certification guarantee cloud sovereignty?
Not necessarily. Cybersecurity can confirm technical protection against threats, but digital sovereignty also involves jurisdiction, operational control, technological independence, reversibility, supply chain security, and protection against external interference.
Why does CISPE talk about “sovereignty washing”?
CISPE uses this term to criticize offerings that appear sovereign without providing verifiable control guarantees. The framework seeks to reduce this confusion through audits, badges, and a registry of evaluated services.
via: cispe cloud