A study presented at Black Hat USA 2024 reveals how Apple’s Wi-Fi positioning system enables global tracking of individuals and military movements
The Black Hat USA 2024 conference has been the stage for one of the year’s most disturbing revelations in cybersecurity and privacy. Researcher Erik Rye, along with a team from the University of Maryland, has demonstrated that Apple’s Wi-Fi Positioning System (WPS) can be exploited to create a massive global surveillance network without users being aware of it.
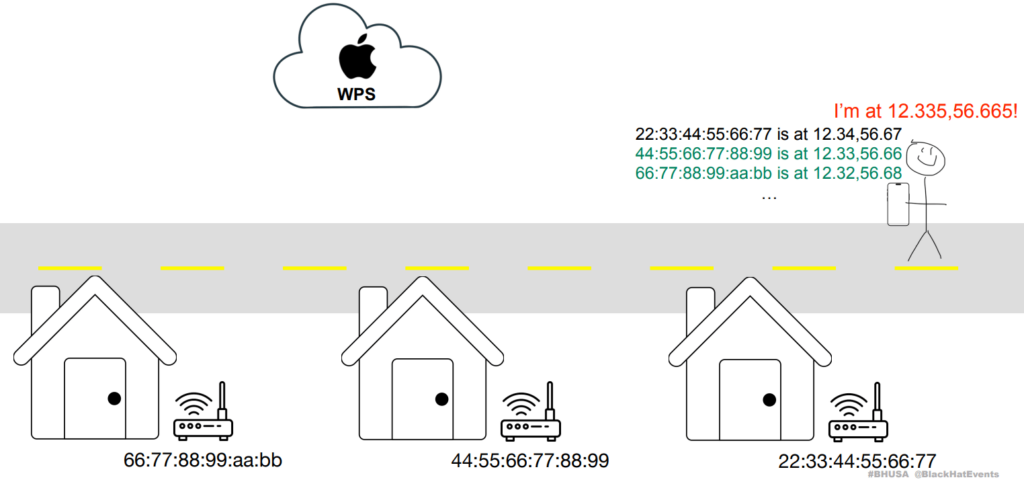
The operation of these systems is simple and well-known: every mobile device with active Wi-Fi detects nearby networks and sends information about them (MAC address or BSSID, network name, signal strength, and GPS location) to the servers of tech giants like Apple, Google, or Microsoft. These databases are used for indoor geolocation, but the study demonstrates that they can also be employed for much darker purposes.
From an open API to global espionage
The Rye team discovered that Apple’s API allowed for mass queries without authentication or strict limits. This meant that anyone, from cybercriminals to foreign states, could query the location of millions of Wi-Fi networks and, with them, track the movement of people and devices.
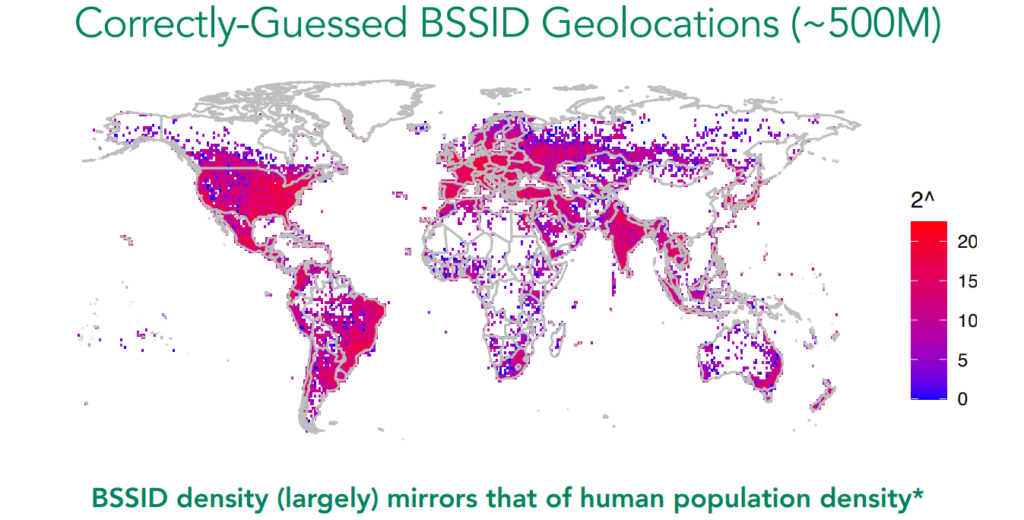
During a year of research, the team collected over 2 billion BSSIDs, building an extremely detailed map of devices and locations worldwide. Moreover, the API returned data from up to 400 nearby access points per request, significantly multiplying the collection capacity.
Real threats and dangerous uses
The report includes practical examples demonstrating how this system can be utilized:
- Military espionage and tracking in conflict zones: Military and civilian movements in Ukraine and Gaza have been tracked without physical intervention, solely through Wi-Fi access point tracking.
- Monitoring after disasters: The sudden disappearance of Wi-Fi networks following the Maui wildfires allowed for assessing the magnitude of the disaster and tracking evacuations.
- Tracking specific individuals: A device continuously associated with a Wi-Fi network can become a mobile beacon, trackable in real-time.
The study also warns of the possibility that companies or governments could build similar databases using wardriving techniques, without needing access to official APIs.
Global impact and lack of regulation
The database compiled by Rye’s team covers densely populated regions and reflects global patterns. The exception is China, where legal restrictions prevent the publication of sensitive geographical data, demonstrating that state control can limit the exploitation of these techniques.
Manufacturers most affected include TP-Link, Huawei, and Vantiva, but the most concerning case is that of Starlink. The satellite routers used by Ukrainian forces were precisely tracked, potentially compromising critical military operations.
Apple’s response and insufficient measures
Following the publication of the research, Apple implemented certain patches: IP limitations, the option for users to opt-out, and partial randomization of BSSIDs. However, researchers agree that these measures do not address the underlying issue.
Erik Rye warns, “The main risk is that any malicious actor, without special permissions, can map the movements of millions of people and critical assets undetected.”
How to protect yourself?
The report recommends manufacturers:
- Dramatically restrict access to their APIs.
- Eliminate responses that return additional data about nearby networks.
- Implement mandatory randomization of BSSIDs in all routers, something that companies like SpaceX have already begun deploying for their Starlink network.
Users are advised to avoid prolonged use of the same router in different locations and, whenever possible, opt for devices that allow for hiding or rotating the MAC address.
The passive surveillance that goes unnoticed
The case presented by Rye confirms what cybersecurity experts have been warning for years: passive geolocation via Wi-Fi is a form of mass surveillance that does not require authorization, consent, or GPS.
In a world where connectivity is ubiquitous, this vulnerability poses a threat to individual privacy, national security, and the technological sovereignty of countries.
A debate that is just beginning
The presentation at Black Hat has sparked a debate in the tech and cybersecurity communities about the extent to which tech giants like Apple or Google should be held responsible for the unintentional exploitation of their infrastructures for espionage purposes.
For now, the data continues to circulate, and the methods to exploit them remain active. The lingering question is: will international regulation be necessary to curb this threat?
References: